If your laptop, Tablet or phone comes with Miracast® technology or WiDi, you can display everything from your device on an HDTV.
We recommend Actiontec ScreenBeam WiDi Receiver around $50 and SUMBOAT wireless display $30 on amazon:
To conference a party into a connected call:
Step 1 Press the Conference button . The call is put on hold.
Step 2 Dial the extension of the party you would like to conference.
Step 3 Press the Confrn soft key to ring the party directly. or Dial the number and press the Conslt soft key to speak with the recipient before ringing him or her into the conference call. After consultation, press the Yes soft key to complete the conference call, or press the Cancel soft key to return to the original two-party call.
Step 4 Repeat to add additional parties.
After a conference is established, you can use the Show soft key to display all
conferenced parties. If you wish to disconnect a party, scroll to the party’s
entry and press the Drop soft key.
With Palo Firewall open, you can
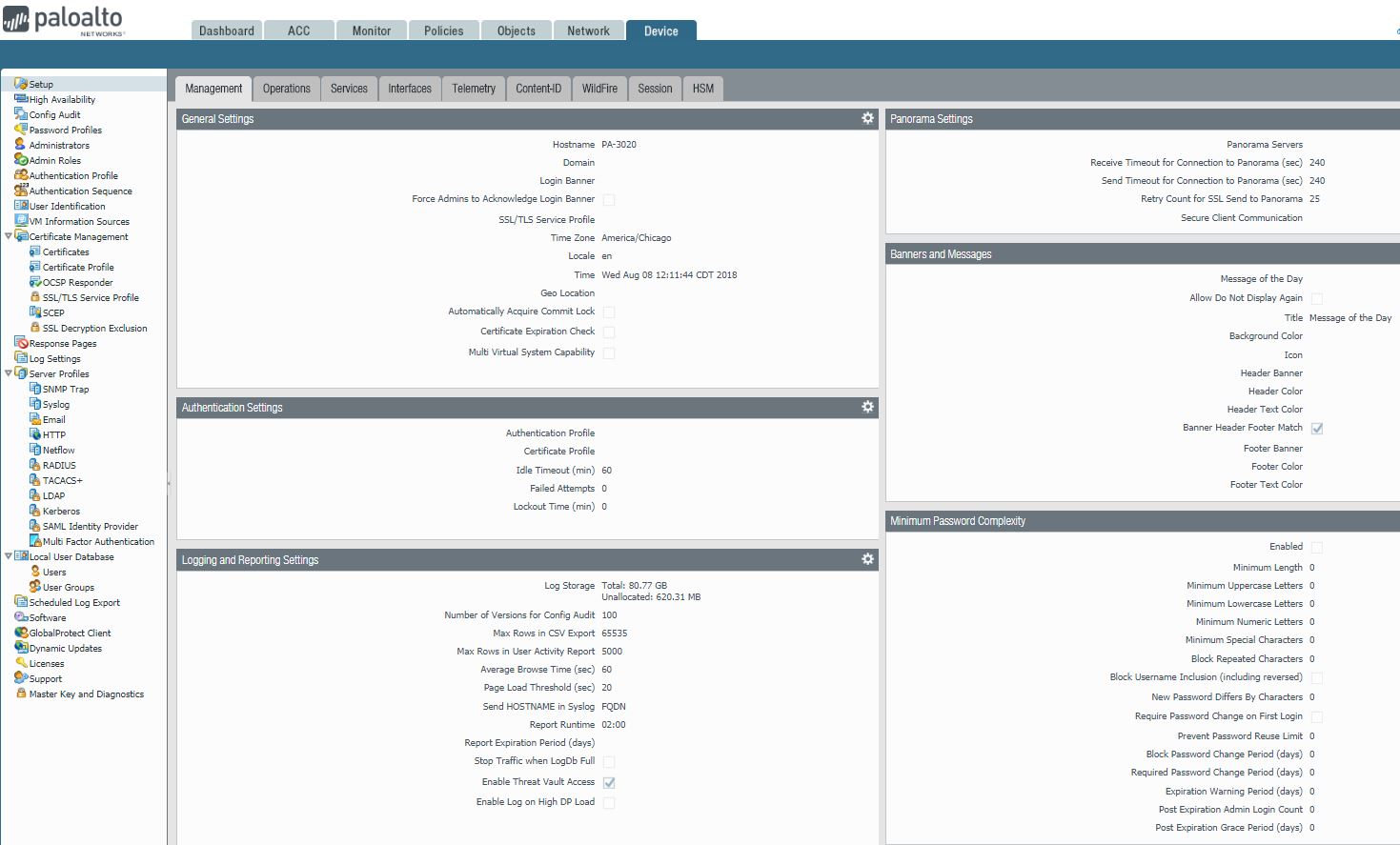
Setup which gives you Management, Operations, Services, Interfaces, Telemetry, Content-ID, Wildfires, Session, and HSM.
configure High Availability.
Add and manage user account.
Certificate Management.
Manage Licenses.
Support.
With Palo Firewall open, we can view and add
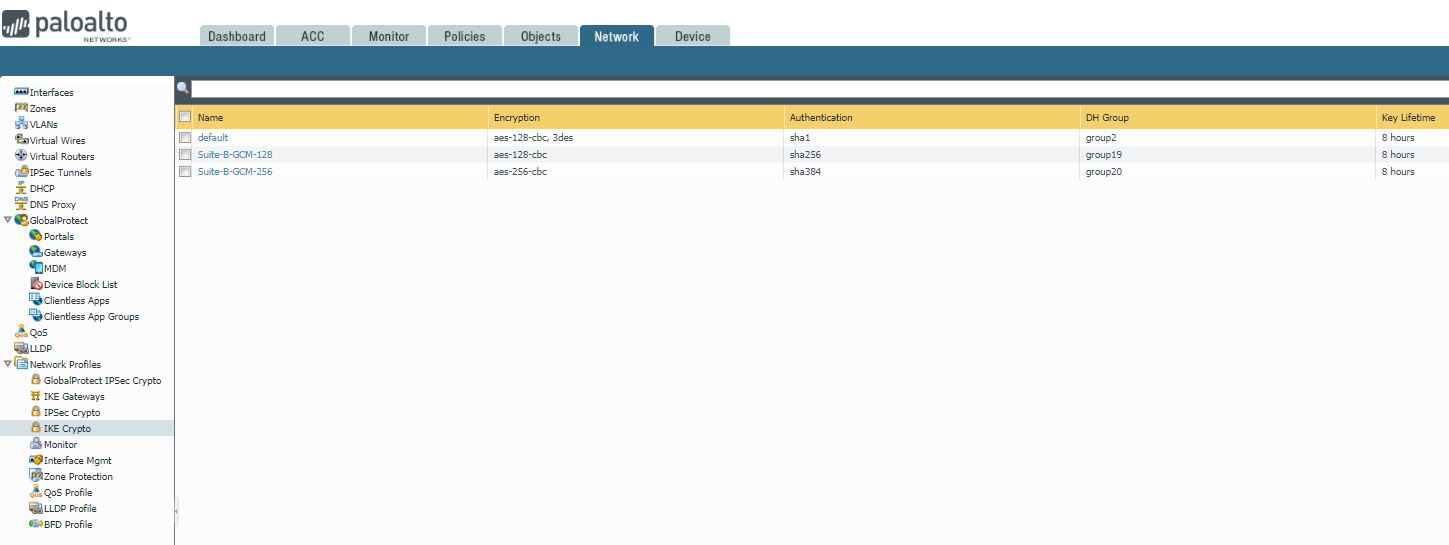
Interface
Zones
VALN
Virtual Wires
Virtual Routers
IPSec Tunnel
DHCP
DNS Proxy
GloabalProtection
Network profiles such as IKE Crypto, Monitor
With Palo Firewall open, we can create these objects:
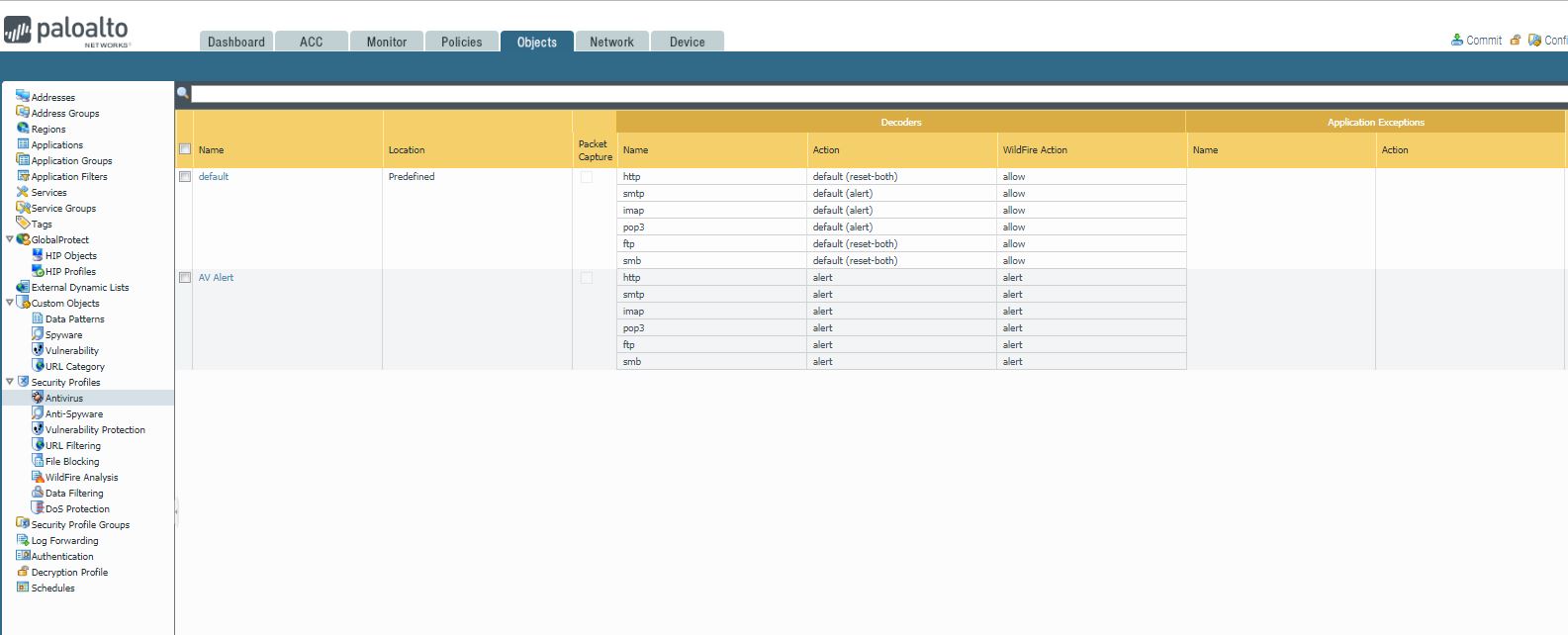
Addresses
Address groups
Applications
Application groups,
Application Filters
Services
Service Groups
Antivirus
Anti-Spyware
Vulnerable Protection
URL Filtering
File blocking
Data Filtering
Security Profile groups
Authentication
Decryption Profile.
With the Palo firewall open, you can
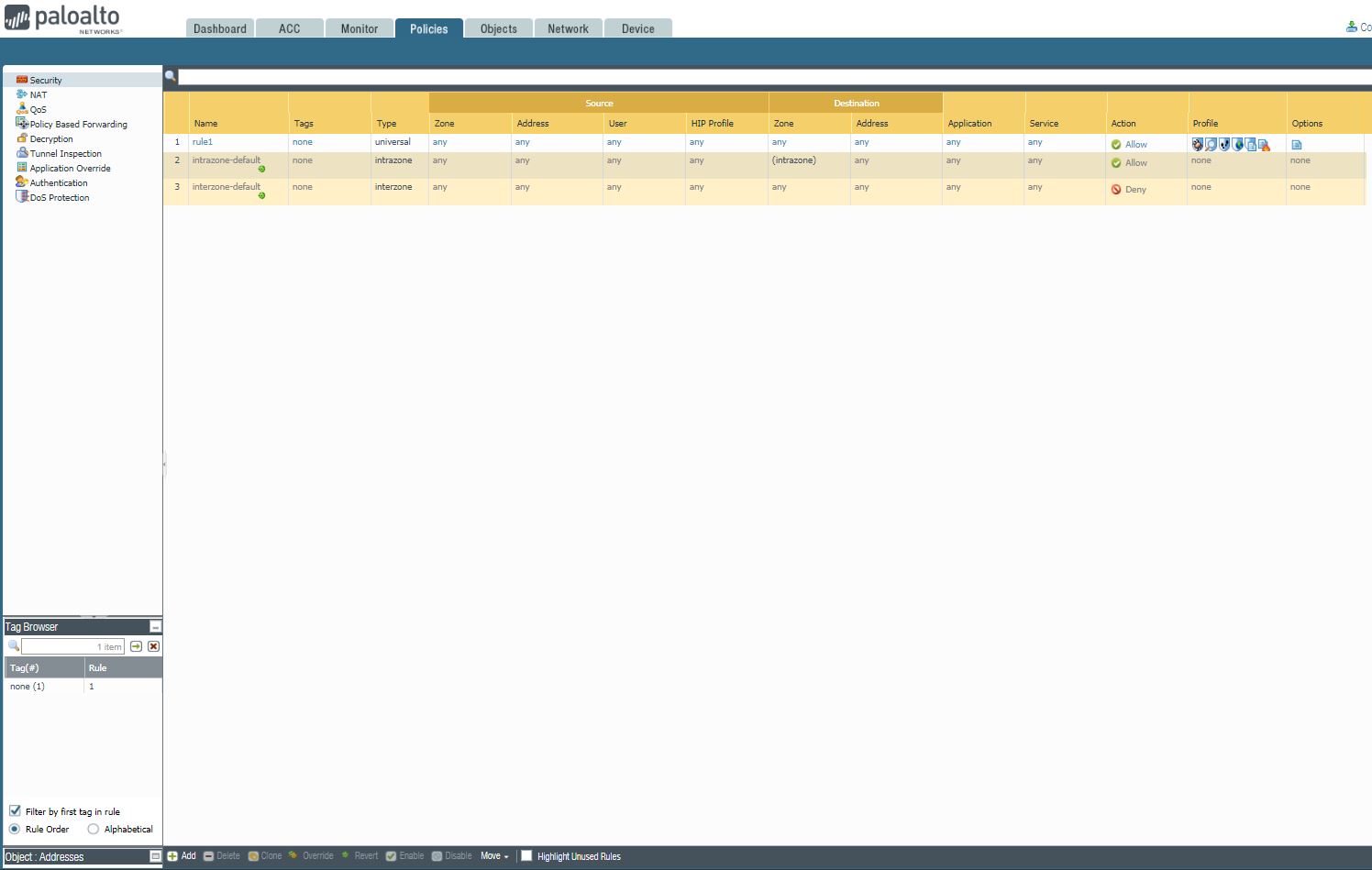
Create Security rules, add NAT, Decryption, Tunnel Inspection, and Authentication.
With Palo Firewall open, click Monitor, you can do these:
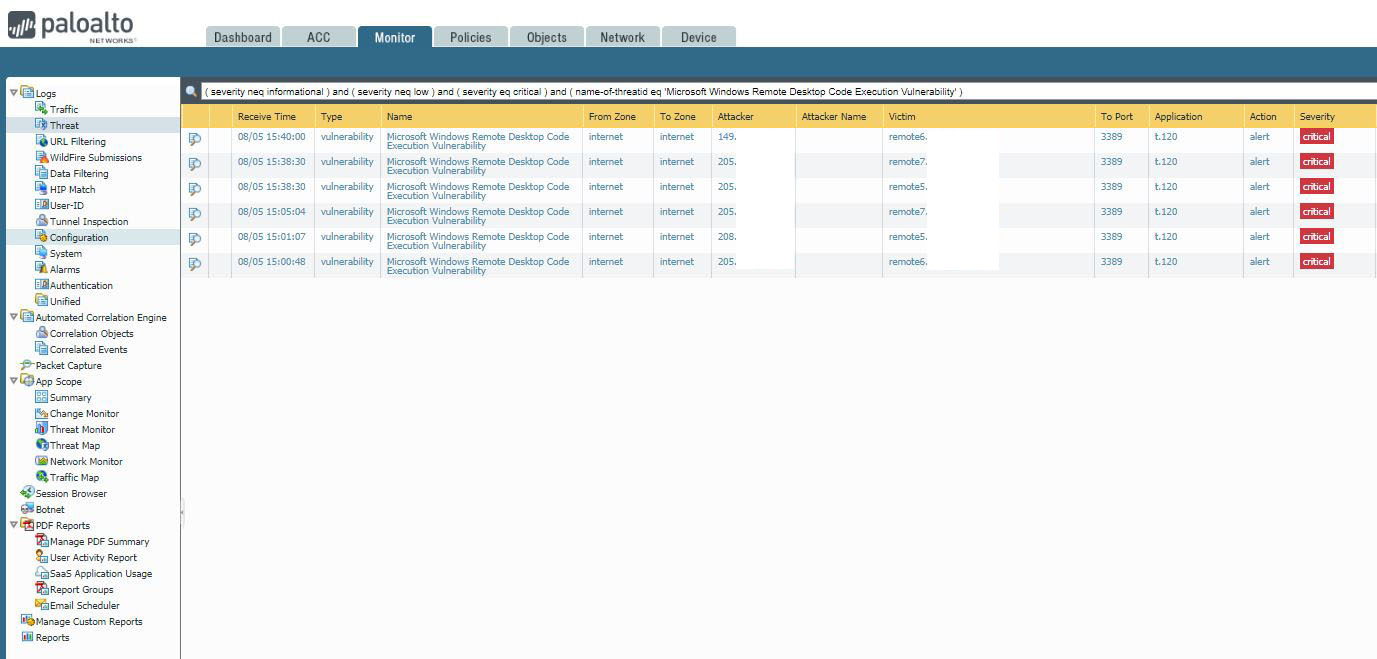
Logs of Traffic, Threat, URL filtering, configuration, system.
Summary of App Scope, Top 10 Apps, Top 10 Threats, Network Monitor of Applications,
PDF Reports, and reports.
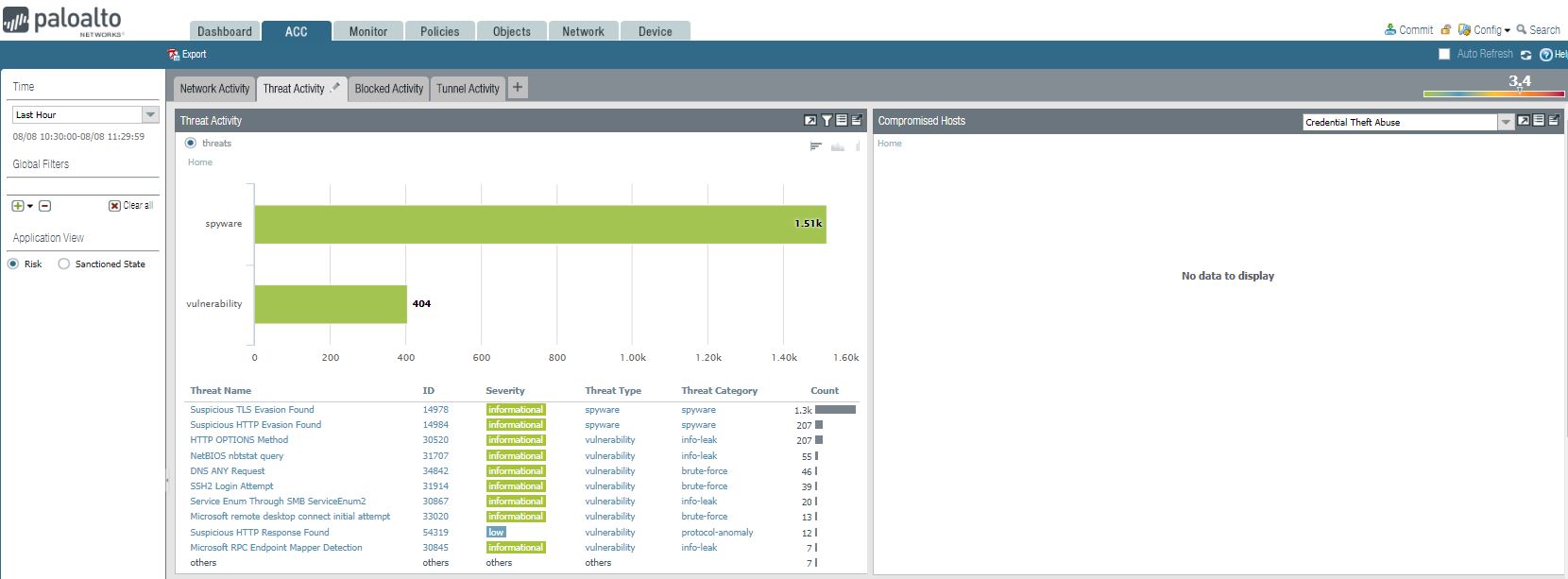
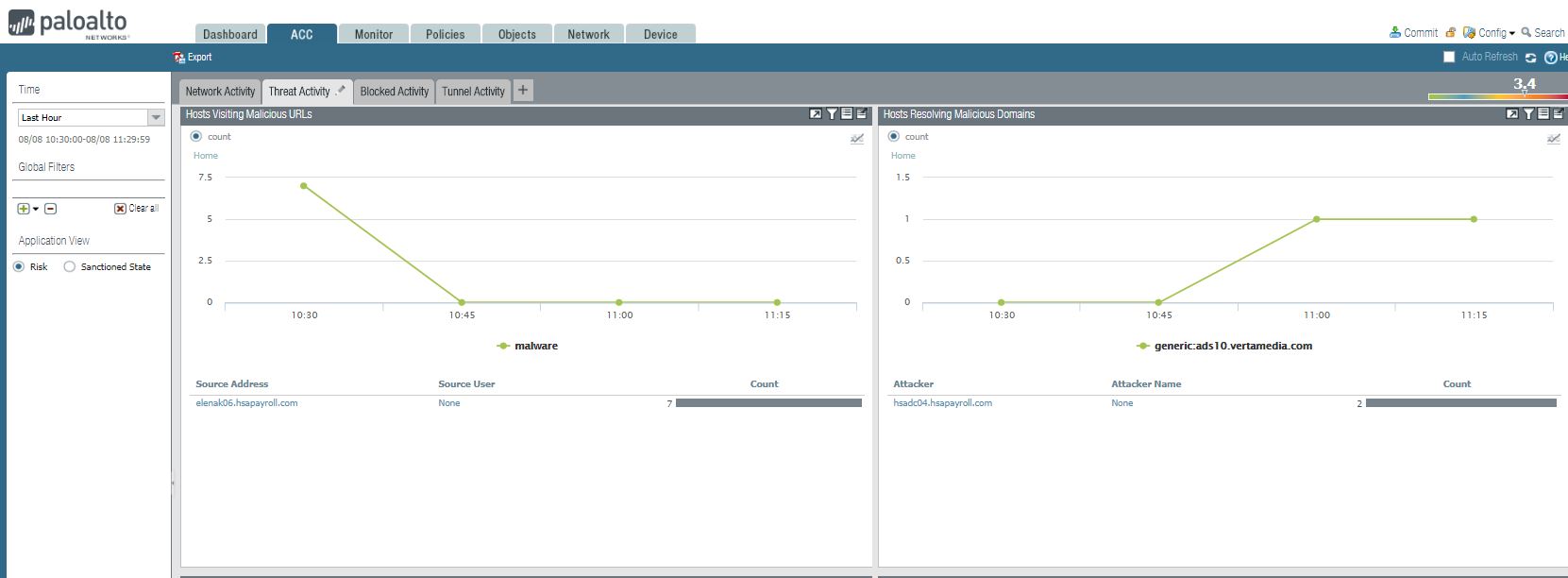
1. We can view Threat Activity and Compromised Hosts.
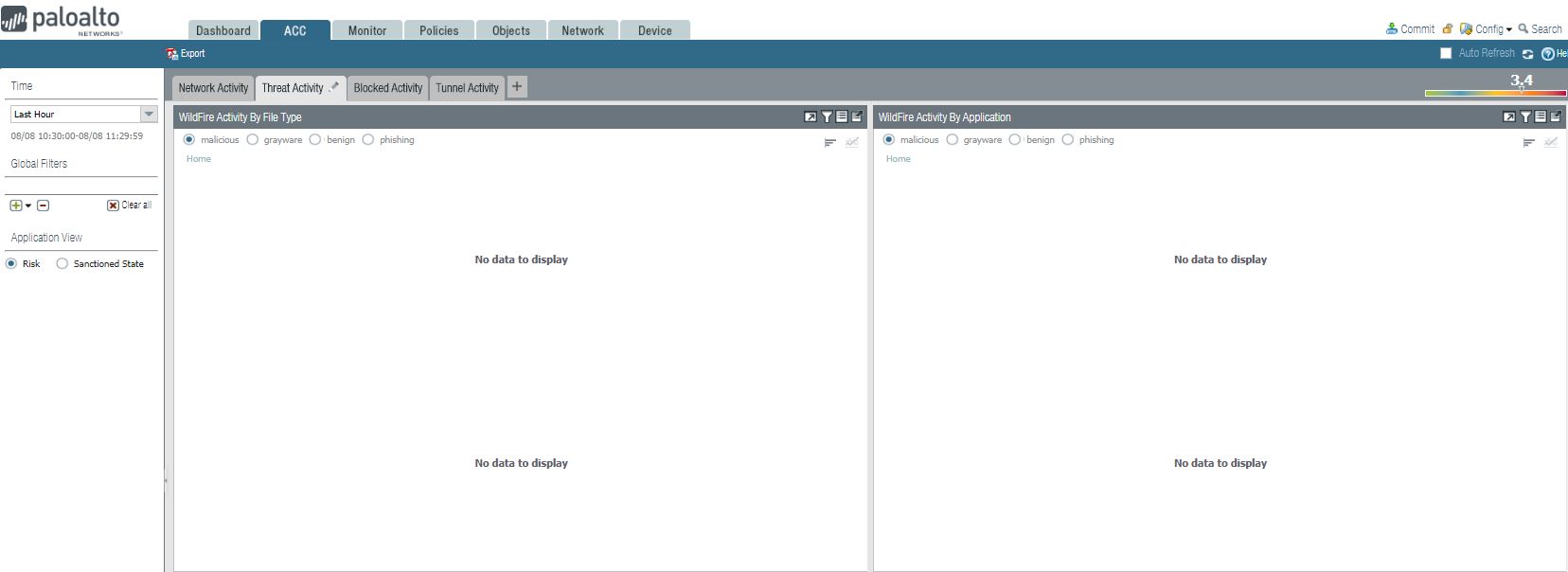
2. We can view WildFire Activity by File Type and WildFire Activity By Application.
3. Hosts Visiting Malicious URLs and Host Resolving Malicious Domains.
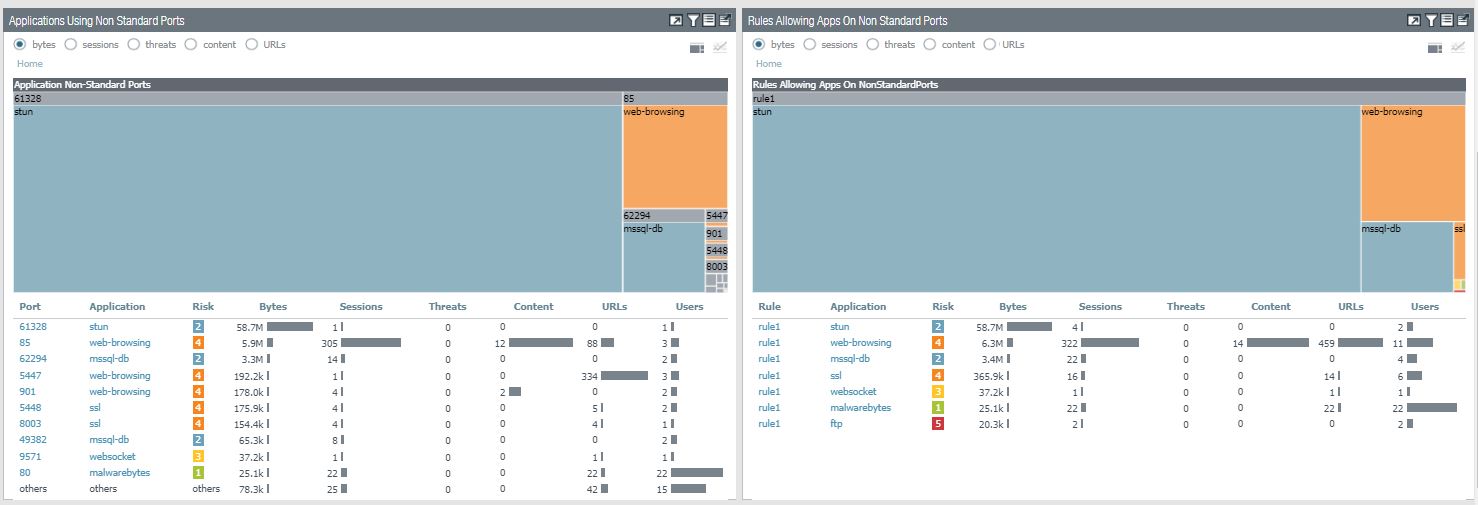
4. Applications Using non Standard Ports and rules Allowing Apps On Non Standard Ports
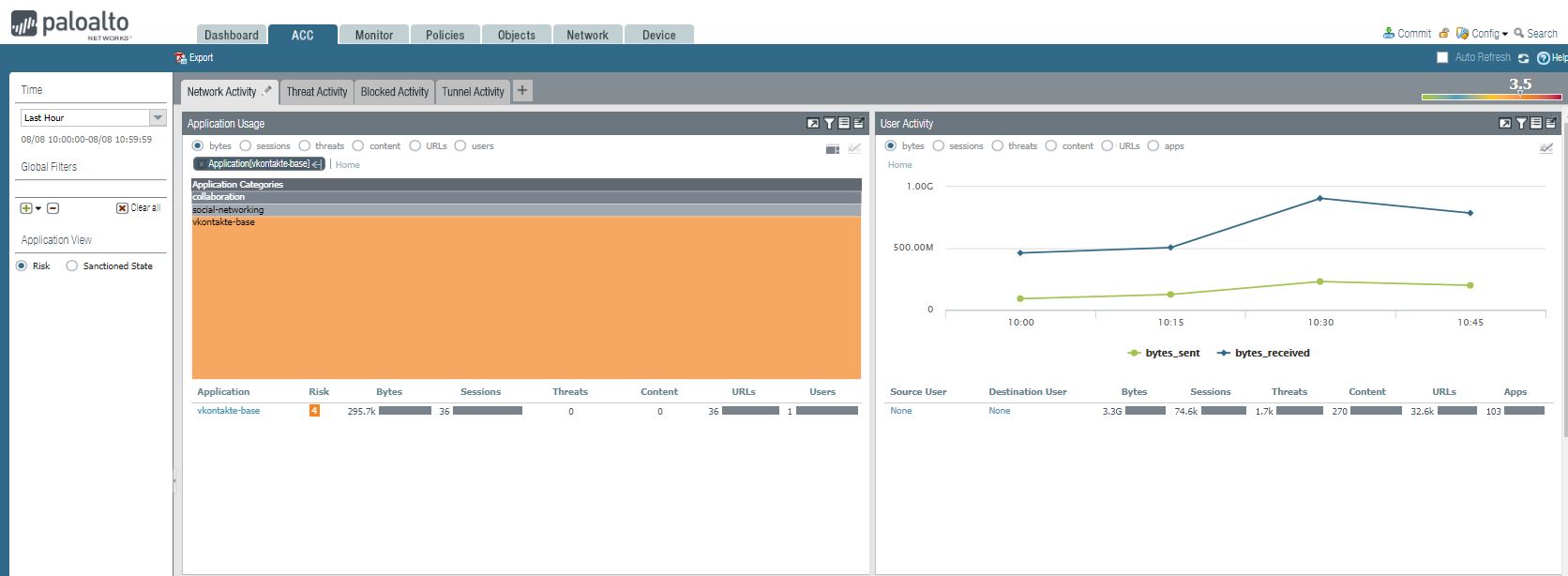
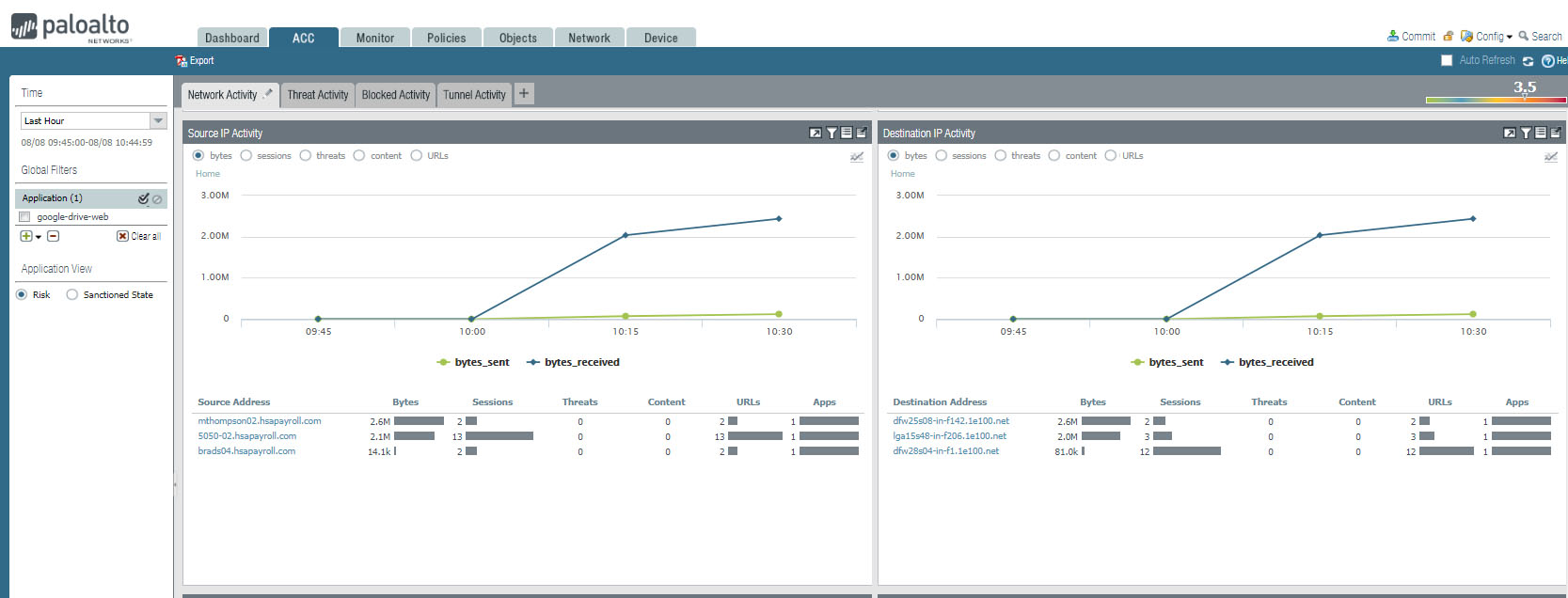
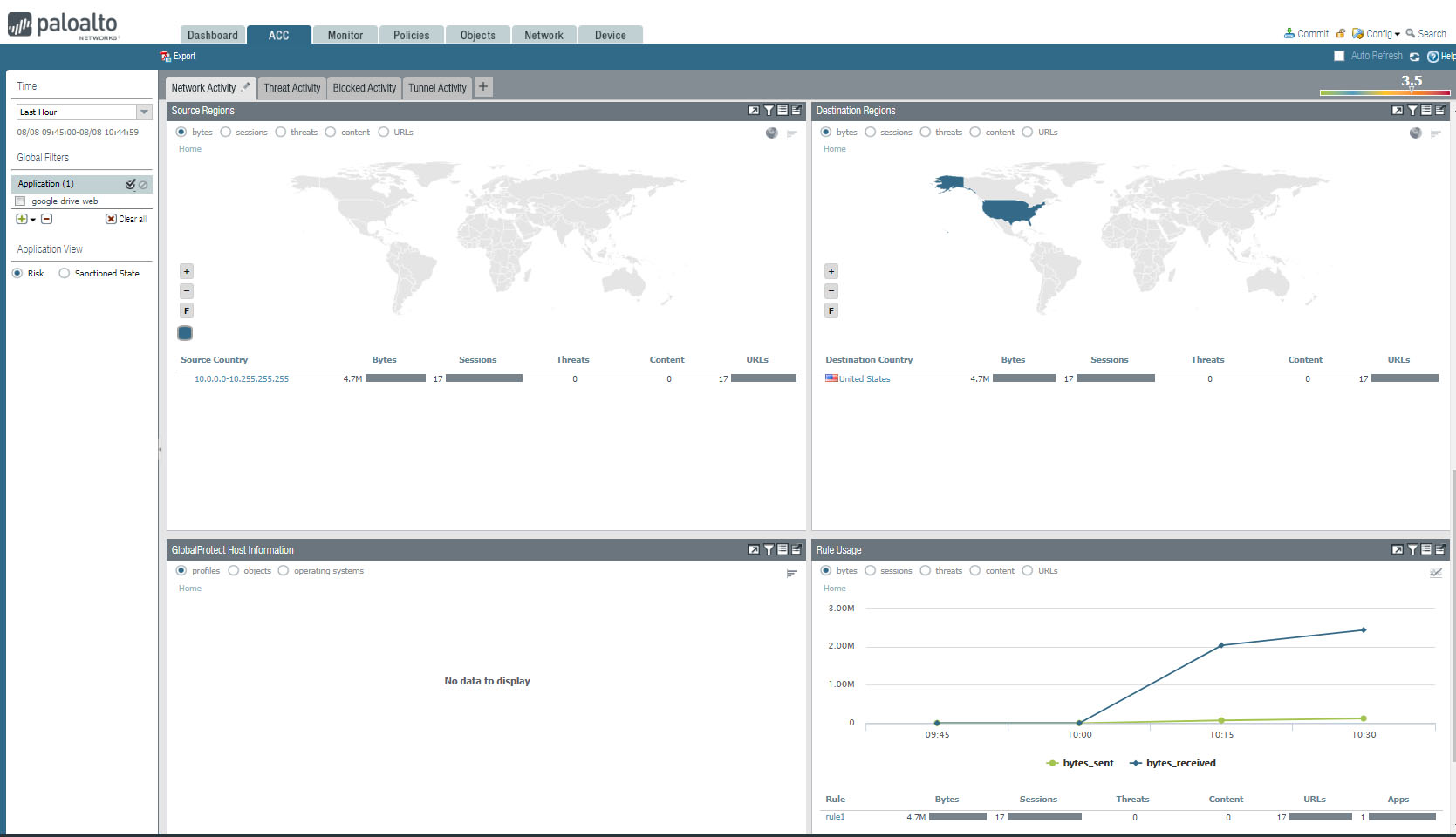
From Palo ACC screen, you can view these information:
1. Application Usage such as Application, Risk Bytes, Session, Threats URLs and users. user Activity such as Source User, Destination User, Bytes, Sessions, Threat, URLs, and Apps.
2. Source IP Activity shows Source address or DNS information.
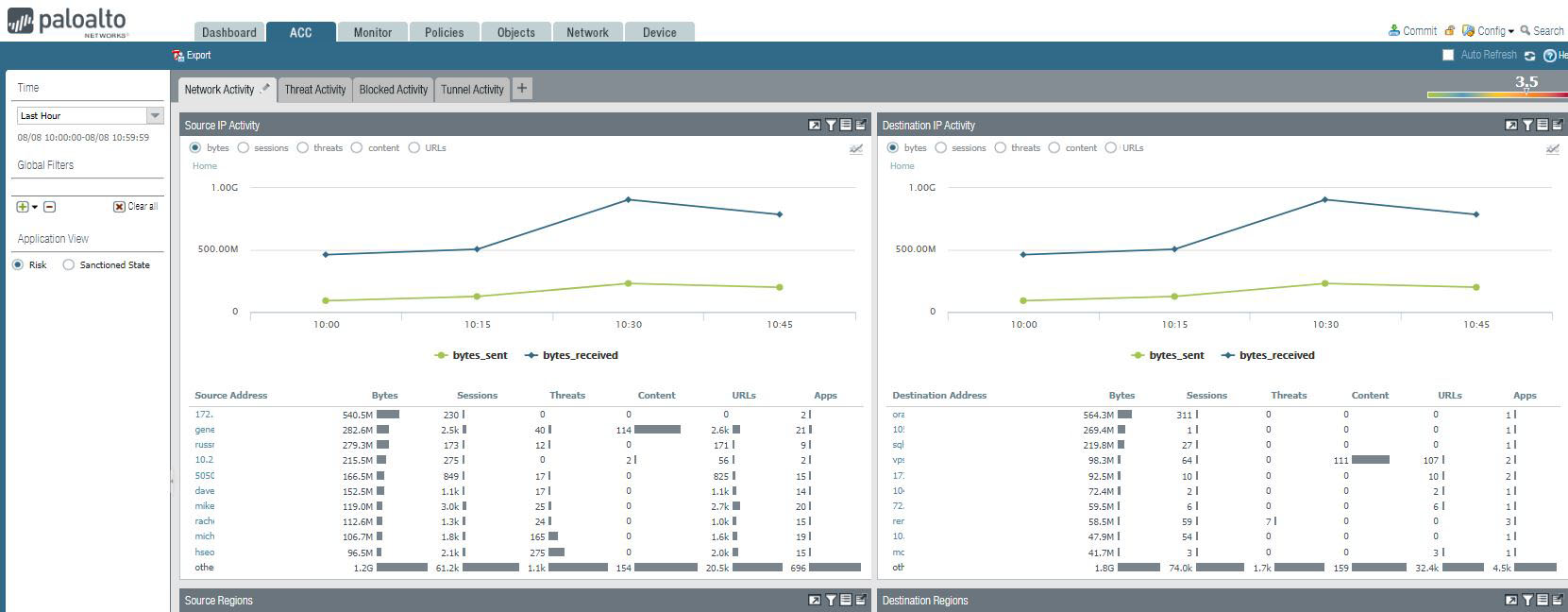
3. Network Activity also shows these information: Source Regions, Destination Regions, GlobalProtection Host Information, and Rule Usage.

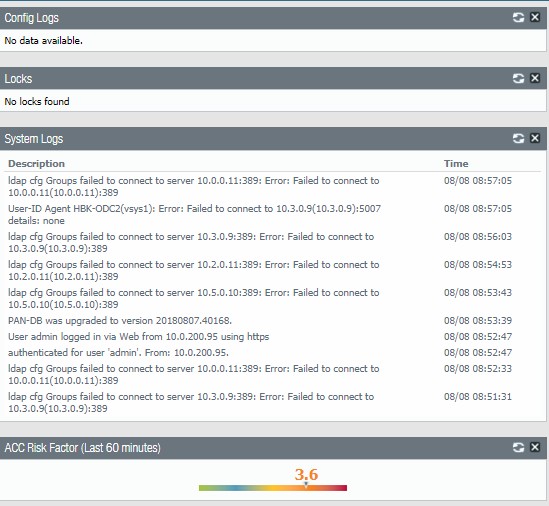
After login Palo, you will have Dashboard looks like this:
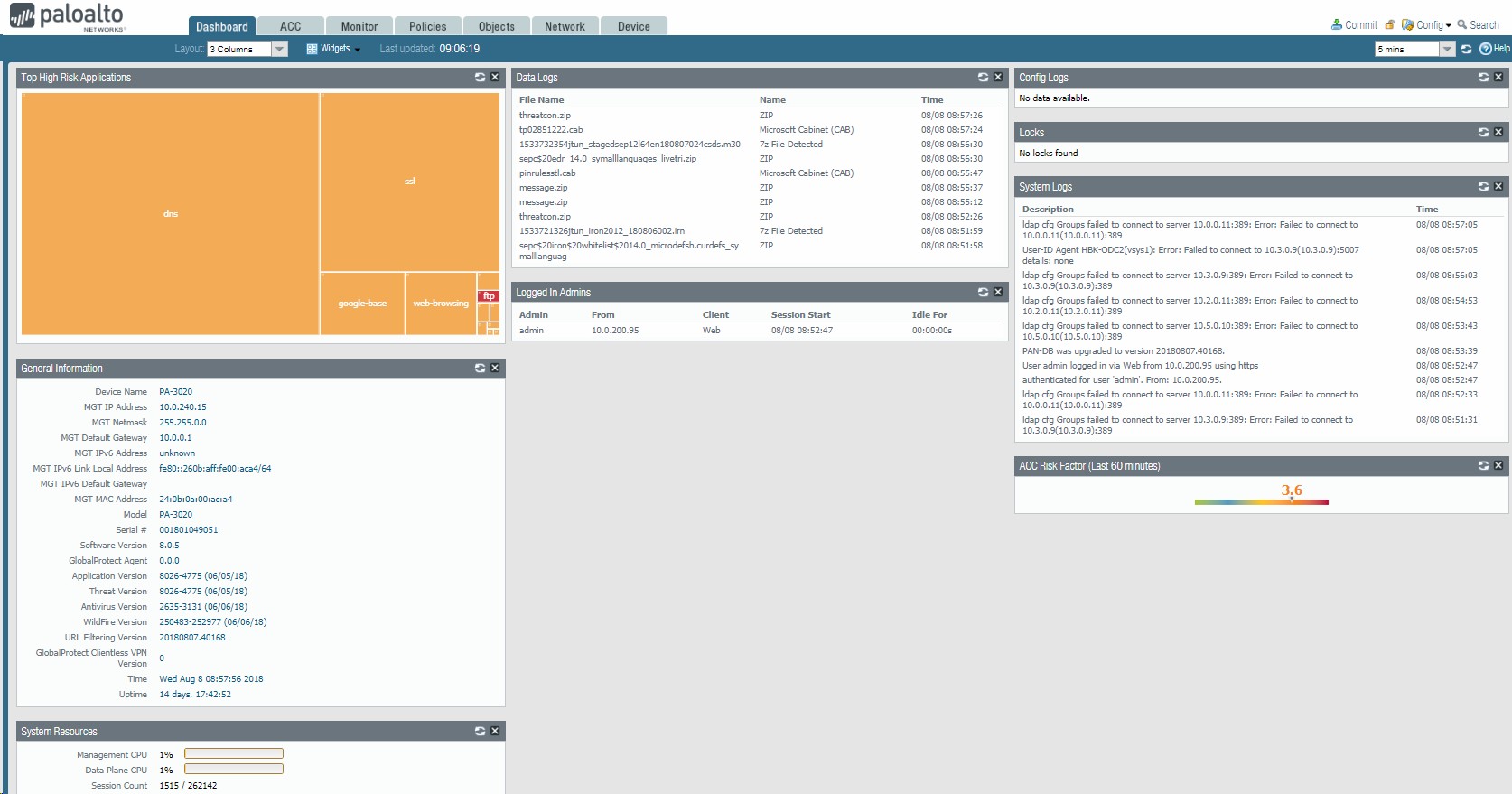
1. You can view Top High Risk Applications and General information such as device IP address, default gateway, Serial #, Software version, time and system resources.
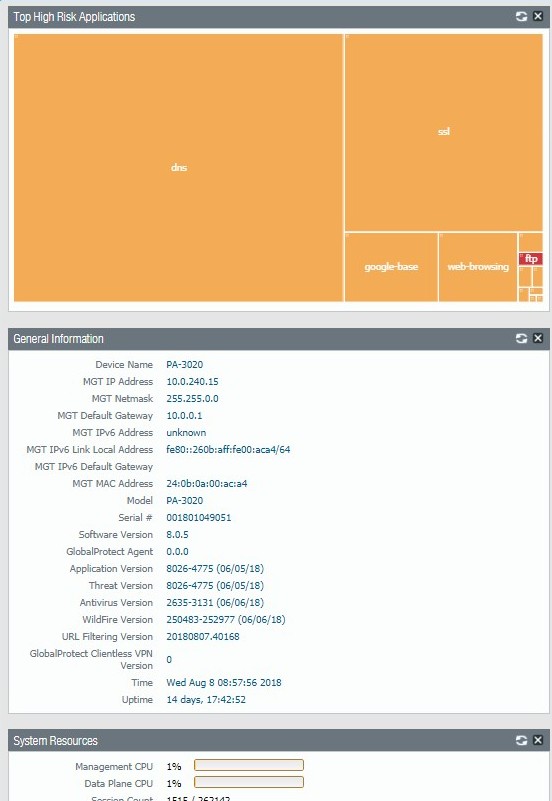
If you click High Risk Applications, it will popup Network Activity. You can High Risk App Usage, user Activity.
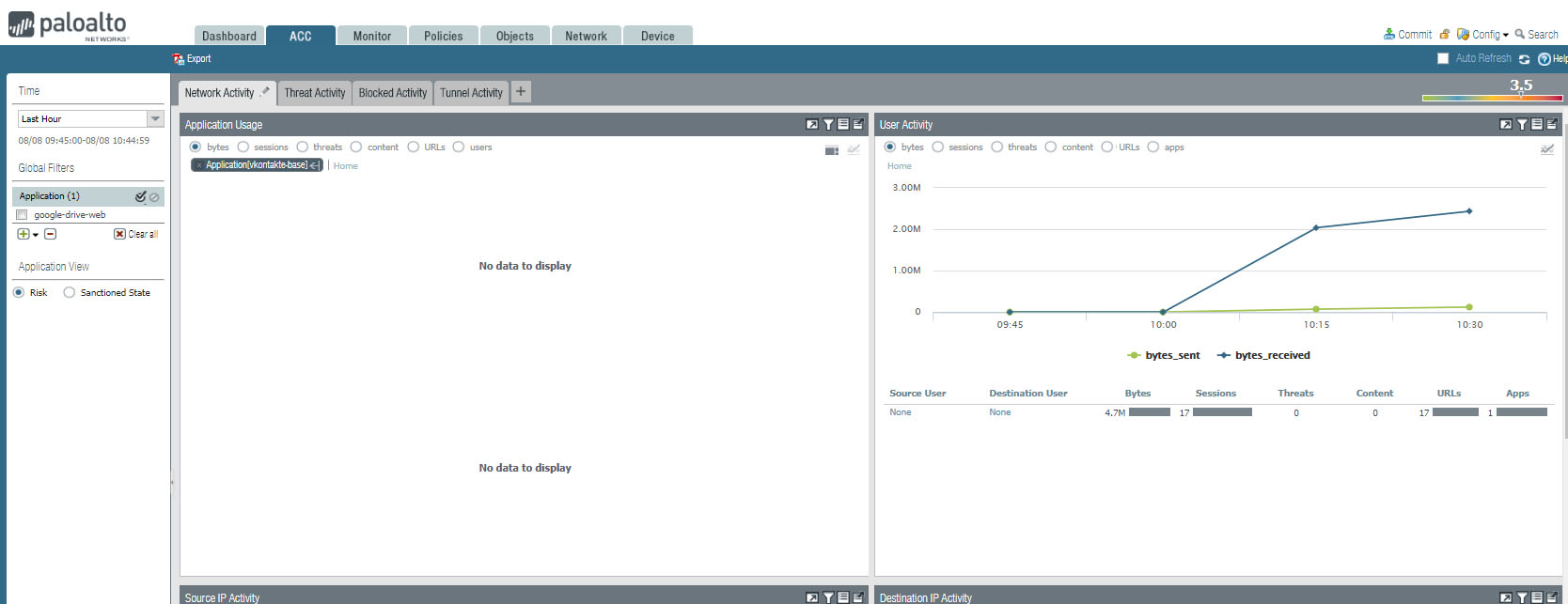
You can also view Source IP Activity, Destination IP Activity, Source regions, Destination Regions.
2. You will have Data logs and Logged In Admins information.
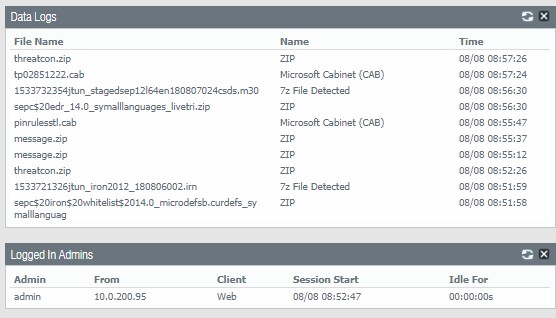
3. You will also have config Logs, Locks. System Logs information.